Glenn Haley, Director of Product Management, Cloudian
The Need for FIPS Validation
In today’s insecure IT landscape and the network-connected world, it is essential to understand how secure your storage system may be, and even more important, to have assurance on the degree of security implemented as the right choice to meet your needs. Ransomware attacks have increased by as much as 4000% with several high-profile attacks such as WannaCry, NotPetYa, and Maze infecting and impacting companies. Standard practices such as using WORM, backups, patching, or secure passwords are all necessary to mitigate the risk of ransomware, but they do not protect the data itself from being accessed and read. The data must also be protected to prevent it from being read if the systems are compromised. To accomplish this, companies and security teams must assess the level of risk and determine the appropriate confidentiality, integrity, and availability required in a company’s security policy.
For confidentiality, encryption is key to keeping sensitive data protected and not viewable by unwanted participants or unauthorized users. However, there are many encryption algorithms, cipher suites, and modes of operation available for providing encryption. To help with such decisions, many enterprise organizations, the public sector, and US federal agencies lean on the implementation of industry standards such as FIPS. Specifically, the FIPS 140-3, a specification established and maintained by the National Institute of Standards (NIST) that defines the critical parameters and security boundaries of protection that vendors must adhere to when using encryption.
Cloudian has recently completed its validation, and NIST awarded a FIPS 140-3 Level 1 certification for our implemented Cloudian cryptographic module integrated as part of Cloudian’s HyperStore object storage platform. Such a certification is significant for Cloudian and reflects the commitments to serving Cloudian customers. The Cloudian HyperStore architecture and native S3 support will continue to play a significant role in the ongoing innovation and expanded use of on-premises S3 cloud object storage in any environment looking to implement stronger security policies to protect their data and IT environments.
What is FIPS 140-3?
The Federal Information Processing Standards (FIPS) Publication 140-2 Security Requirements for Cryptographic Modules (FIPS PUB 140-2) is a standard developed by the National Institute of Standards (NIST) and is widely used to approve cryptography related algorithms and cryptographic modules. Meeting these standards is required to sell into various governmental and federal agencies, such as the Department of Defense (DoD). Further, an increasing number of large companies, healthcare entities, and financial institutions have turned to FIPS compliance, certification, and validation as a way to meet their security needs.
Why is FIPS 140-3 important?
Encryption is key to providing confidentiality and protecting customer sensitive data. Both symmetric and asymmetric methods can be applied, and many different cryptographic algorithms are available that can encode (i.e., encrypt) and convert plain text into unreadable ciphertext without having the appropriate keys. Understanding the many different methods and algorithms and evaluating solutions can be quite challenging when various software components and cryptographic modules and services are involved. Being FIPS validated ensures that the encryption methods used have been independently reviewed and tested before being deployed. FIPS is also a mandatory requirement among most US federal agencies, many foreign governments (including the European Union, South America, and Asia), and other regulated industries around the globe.
Section 5131 of the Information Technology Management Reform Act of 1996 mandated the use of FIPS-validated products by all DoD and U.S. federal agencies. Also, the Federal Information Security Management Act of 2002 (FISMA) mandates that U.S. government departments and agencies use FIPS 140-3 validated cryptographic modules for security applications. FIPS is also a prerequisite before achieving a Federal Risk and Authorization Management Program (FedRAMP) approval within many sponsored US government and federal facilities within the US and Canada.
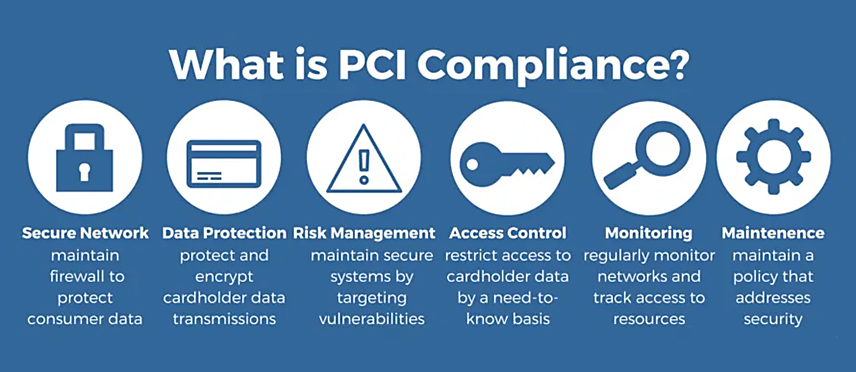
Most industries outside the public sector require securely storing and processing sensitive data. In the financial and banking industries, the FIPS standard has been adopted as a reasonable way to satisfy the requirements of the Payment Card Industry Digital Security Standard (PCI-DSS). Similarly, FIPS is widely used in the healthcare industry that must secure and ensure the privacy of patient data required by the Health Information Technology for Economic and Clinical Health Act (HITECH).
What is involved and how is FIPS 140-3 validation achieved?
The National Institute of Standards and Technology (NIST) is responsible for defining and maintaining the FIPS 140-3 standards and publications. The FIPS 140-3 standard requires that any hardware or software cryptographic module only implement approved algorithms, symmetric and asymmetric encryption techniques, and the use of hash standards and message authentication. Thus, any cryptographic module being considered for validation must only use the approved algorithms on the NIST FIPS list or demonstrate a secure way to turn off any unapproved algorithms, so they are not accessed and used.
To achieve a FIPS 140-3 certification or validation means that one of 22 NIST specified laboratories, as part of their National Voluntary Laboratory Accreditation Program (NVLAP), actively validates the vendor’s product to comply with the FIPS 140-3 standard. NIST then issues one of four security levels for the cryptographic module. Software-only Level 1 validation is deemed sufficient for most government and federal agency use.
NIST awarded Cloudian FIPS 140-3 Level 1 validation after Advanced Security Labs, who is an independently accredited NVLAP located in San Jose, California, reviewed, tested, and assessed the Cloudian implementation and its use of the FIPS-approved algorithms and cryptographic module. With a FIPS 140-3 Level 1 implementation, NIST has validated that the product has a secure boundary established around our cryptographic module when using the Cloudian cryptographic module integrated into the HyperStore 7.2.x software and later release versions.
Cloudian tested various algorithms and sent the vector results to NIST for review as part of the Cryptographic Algorithm Validation Program (CAVP) and Cryptographic Module Validation Program (CMVP).
The Cloudian NIST validation certificates are available on the NIST website:
CAVP Certificate #C3161 (issued on November 16, 2019): https://csrc.nist.gov/projects/cryptographic-algorithm-validation-program/details?product=11747
CMVP Certificate #3663 (issued on May 29, 2020): https://csrc.nist.gov/Projects/cryptographic-module-validation-program/Certificate/3663
About Cloudian FIPS Implementation
Companies require encryption for both data in motion and data at rest. Data-At-Rest encryption delivers a secure layer of protection to ensure data privacy for confidential or sensitive data. Encryption can make sure that stored data remains safe even if the physical media is lost, stolen, or falls into the wrong hands. Cloudian’s software-based encryption with native key management offers an easy way to ensure FIPS 140-3 validated data security.
Cloudian HyperStore has several options for delivering data-at-rest encryption, and now these solutions comply with FIPS 140-3 standards. Cloudian worked with an accredited NVLAP partner (Advanced Security Labs) to help complete the NIST validation and receive our FIPS 140-3 certification. The OpenSSL FIPS Object Module 2.0 as a FIPS-compliant cryptographic module component was integrated and helpful in accelerating the validation process to only less than a year in total.
Cloudian’s native software-based encryption utilizes FIPS 140-3 Level 1 validated algorithms by implementing a FIPS validated cryptographic module. Customers can enable encryption at any time during their HyperStore deployment and without impacts; performing Cloudian Server-Side Encryption (SSE) encryption in the background does not degrade performance nor disrupts any of the HyperStore services or S3 client applications.
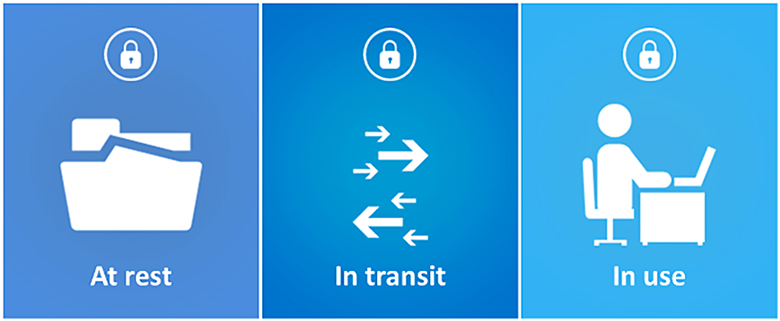
Data at rest and data in-flight encryption are requirements for many institutions and agencies. Many storage solutions employ self-encrypting drives (SEDs) to meet data at rest encryption requirements. However, this method only protects data on the drives themselves when the drives have been powered off, thus only providing data protection only if the drives have been stolen or misplaced. For data encryption to properly ensure confidentiality, the data should be protected even if the attackers are on the network, attempting “man in the middle” attacks, or able to extract data off the system or network. Re-keying and key-destruction provide methods to effectively crypto-erase exfiltrated data making it useless to any attacker.
Only a few object storage vendors have achieved a FIPS 140-3 validation from NIST. Upon investigation, only one other known vendor has implemented a FIPS-approved cryptographic module into their products to perform their FIPS 140-3 validation. Instead, most vendors simply rely on the use of FIPS-approved self-encrypting hard drives (SED) to claim FIPS support. For some customers, this is not enough to meet their strict requirements. In contrast, Cloudian is committed to ensuring the highest levels of security for our customers and has achieved both a Common Criteria EAL2 designation and a FIPS 140-3 Level 1 validation – where again, only one other vendor can claim that accomplishment. These, combined with ObjectLock WORM functionality and successful assessments and certifications such as SEC17a-4(f), FINRA Rule 4511, and CFTC Regulation 1.31 compliance, establish Cloudian’s leadership position for security among object storage vendors.
Will future upgrades impact our FIPS-validated status?
The rules that each vendor must follow to achieve the FIPS 140-3 certification are stringent. Any component involved in the cryptographic processing of data must be securely designed, documented, tested, and then reviewed and validated by the NIST Testing Laboratory.
Once FIPS certified, any modifications to an encryption component cannot be made without a re-certification by NIST. Any change to a FIPS-validated product in any way (including software patching) will result in it losing its certification, and the solution will need to be re-certified. Depending on the degree and amount of changes that made to the design, the recertification process with NIST can be even longer than the initial review cycle.
However, this is not a concern for the Cloudian HyperStore software. Cloudian achieved its FIPS 140-3 validation based on the implementation of an open-source FIPS-approved cryptographic module. Hence, any changes to the Cloudian HyperStore software with the consistent use of the integrated Cloudian cryptographic module can occur without impacts to the awarded FIPS validated status.
How do I enable FIPS with Cloudian HyperStore?
Cloudian customers can contact the Cloudian Support team or their local System Engineer to learn more about upgrading the HyperStore system software to a version that includes the FIPS-certified cryptographic module. There is no cost for the Cloudian cryptographic module, which is a standard feature and functional component starting with the Cloudian HyperStore 7.2.1 GA software release.
Conclusion
Implementing the NIST approved encryption algorithms allows regulated industries and government agencies to be confident in a product’s security implementation. Cloudian’s FIPS certificates validate and enable our customers to meet higher-level security requirements using the Cloudian HyperStore as a secure object storage solution.
The Cloudian HyperStore object storage is deployed in many of the world’s largest service provider environments and is installed at hundreds of companies and organizations to deliver S3 compliant cloud storage. The Cloudian HyperStore is ideal for regulated security environments such as federal and public sectors, as well as healthcare, finance, and other industries where FIPS 140-3 data security is required.
Sources
https://csrc.nist.gov/publications/detail/fips/140/2/final
https://csrc.nist.gov/csrc/media/publications/fips/140/2/final/documents/fips1402annexa.pdf
Learn More
Learn more about the rich set of security functionality in Cloudian HyperStore here.