Understanding HIPAA Compliant Cloud Storage and On-Premises Alternatives
The US HIPAA regulation applies to healthcare providers, healthcare professionals, insurance companies, and many other organizations, including anyone who provides business services to these Covered Entities (CE). Protected Health Information (PHI) is increasingly digitized, and the exploding volume of protected data raises the question of how to store the data in a way that is HIPAA compliant and conducive to protecting data privacy and security.
Read on to learn the basics of HIPAA compliance, how it applies to storage both on-premises and in the cloud, HIPAA compliance offered by the major cloud storage services, and how you can achieve cloud-like benefits with HIPAA compliance on-premises. As you read on you will learn the important role HIPAA compliance plays in health data management.
In this article you will learn:
• HIPAA compliance terminology
• HIPAA requirements for cloud storage
• HIPAA compliant cloud storage by the major cloud vendor
• Keeping healthcare data on-premises without giving up cloud benefits
Read more in our guide to storing your healthcare data.
HIPAA Compliance Terminology
The Health Insurance Portability and Accountability Act (HIPAA) is a US regulation that requires organizations dealing with Protect Health Information (PHI) to keep that data secure. HIPAA is a mandatory standard and there are fines and penalties up to a cap of $1.5 million per year.
Here is a brief guide to HIPAA terminology:
Protected Health Information (PHI)
PHI, as defined by the HIPAA Privacy Rule, includes the following information, in electronic, paper or oral form: an individual’s past, present, and future health conditions, health care provided to a patient, payment information, birth or death dates, patient contact information: telephone numbers, addresses, and more, social security numbers, and any other identifying information.
Covered Entities and Business Associates
A Covered Entity (CE) is an individual or organization that uses or comes in contact with PHI. These are typically healthcare providers, healthcare professionals like doctors and nurses, nursing homes, insurance companies, and their employees. A Business Associate (BA) is an organization or person providing services to a covered entity – for example, providing IT services or legal services. BAs are also responsible for HIPAA compliance but have different regulatory requirements than CEs.
HIPAA Privacy Rule
The HIPAA Privacy Rule explains who is allowed to access PHI and how by whom and in which circumstances it should not be accessed.
HIPAA Security Rule
The HIPAA Security Rule specifies what Covered Entities and Business Associates need to do to manage and secure electronic PHI, and ensure its confidentiality and integrity. This includes administrative measures (such as a policy specifying only caretakers can view PHI for their patients), physical measures (such as physically securing a facility or cabinet storing PHI) and technical safeguards (such as an authentication system preventing unauthorized staff from viewing electronic medical records).
HIPAA Breach Notification Rule
The HIPAA Breach Notification Rule requires Covered Entities to notify patients and the Department of Health and Human Services (HHS) is their IT systems are breached. Data breaches affecting more than 500 people must be disclosed within 60 days, publicized in the media and prominently posted on the organization’s website.
HIPAA Omnibus Rule
The Omnibus Rule is a revision to the HIPAA regulations that expanded HIPAA to cover more organizations, who are now defined as Business Associates for the purposes of the law. These include subcontracts, consultants and computer storage companies. The rule also added new provisions such as limiting the use of genetic data for insurance and the use of PHI for marketing purposes.
HIPAA Requirements for Computer Storage
Electronic PHI (ePHI) needs to be stored somewhere, and so the form of computer storage you use, whether it is on-premise storage or cloud storage, must be HIPAA compliant.
Some cloud storage providers say they support HIPAA, meaning they comply with the privacy and security rules. But typically, responsibility for compliance is shared with the storage user, and it is the user’s responsibility to configure cloud services in a way that will be HIPAA compliant.
Cloud vendors may or may not be willing to sign a business associate agreement (BAA), which confirms that they meet all HIPAA requirements related to physical security, digital security, privacy, backup, authentication and administrative measures. If the vendor does not sign a BAA, the organization using the cloud services may be at risk of noncompliance in case of an audit.
Let’s cover how HIPAA rules apply to storage.
| HIPAA Rule | On-Premise Storage | Cloud Storage |
| Privacy Rule | Storage devices are affected if they store any form of PHI | Cloud services are affected if they store any form of PHI |
| Security Rule | CEs or BAs maintaining storage devices must ensure the appropriate safeguards. | CEs or BAs using cloud storage must ensure that the cloud vendor has the appropriate safeguards in place – the best way to do this is by signing a BAA. |
| Breach Notification Rule | The organization whose systems were breached is required to notify. | Both the organization owning or managing the data and the cloud provider is required to notify about a breach. |
Related content: Read our guide to medical records retention
HIPAA Compliant Cloud Storage by the Major Cloud Vendors
The following table summarizes HIPAA compliant storage offered by the major public cloud and storage providers.
| Provider | Willing to Sign BAA? | Compliant Services | Responsibility of Covered Entity |
| Yes | G Suite, Google Cloud Platform | Creating a secure environment for applications built-in Google Cloud Platform | |
| Microsoft | Yes | Azure and Azure Government, Office 365, Dynamics 365, PowerApps, PowerBI, and more | Ensuring it has a compliance program and internal processes and using Microsoft services in line with HIPAA |
| Amazon | Yes | Amazon S3 Glacier | Amazon also signs a BAA for AWS services in general but requires customers to set up HIPAA-compliant cloud storage, in line with the Amazon reference architecture |
| Box | Yes | All storage services | Administrative processes for protecting PHI |
| Dropbox | Yes | Dropbox for Business | Administrative processes for protecting PHI |
On-Premises Storage for Healthcare: Keeping Data On-Premises Without Giving Up Cloud Benefits
Healthcare organizations and their business partners typically do not migrate all data to the cloud. Although HIPAA-compliant cloud services exist and are in widespread use, there is always a need to retain some, if not most, of ePHI data on-premises. At the same time, cloud services provide tremendous benefits like scalability, ease of management, and improved strategies for backup and disaster recovery.
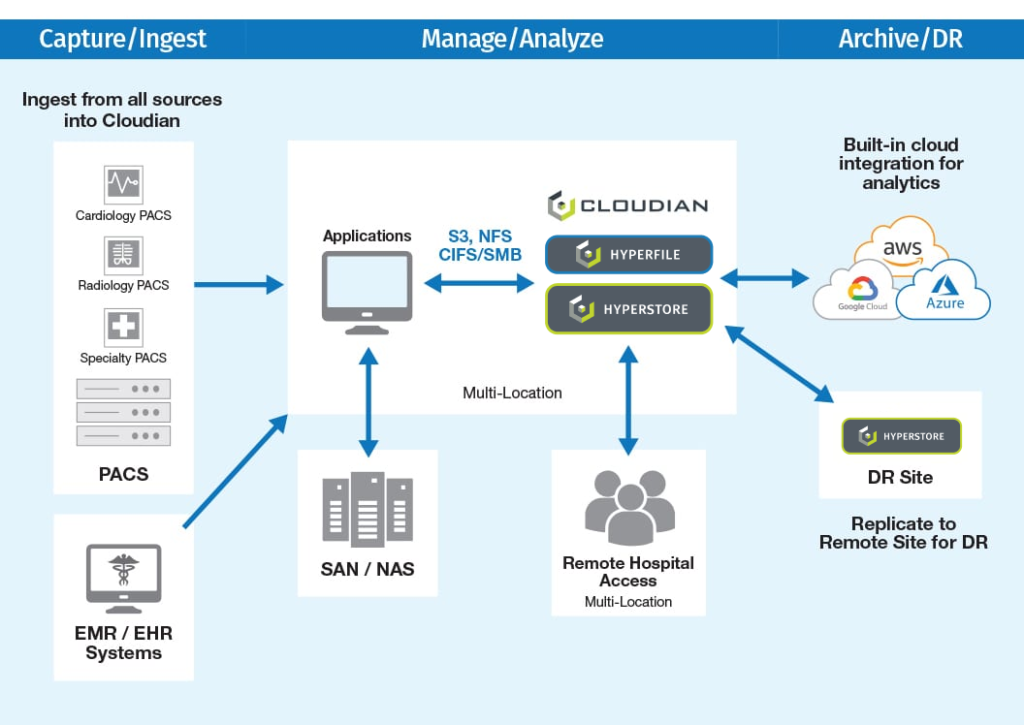
Cloudian addresses these requirements with HyperStore, an exabyte-scale, on-premise storage platform for healthcare environments. HyperStore makes it possible to store, move and protect files across locations at up to 70% lower cost than disk-based storage, with the convenience and scalability of cloud services, and with full compatibility with public cloud services like Amazon S3.
Hyperstore is fully HIPAA compliant, with security features including data encryption and transparent key management, AES-256 server-side encryption for data at rest, SSL for data in transit, RBAC with specified levels of access, audit trail logging, WORM (Write Once Read Multiple) for storage of immutable data.
The Cloudian platform provides the following benefits for healthcare organizations:
- Cloud flexibility—deployments can start small and grow as needed, from a 3-node configuration to thousands of nodes as needed. Each node can be a physical appliance or virtual, running on commodity hardware.
- Broad integrations—HyperStore integrates with numerous healthcare applications and archive solutions, allowing it to be used as a central repository, with access to a complete view of patient information.
- Rich metadata—HyperStore has rich metadata tagging features built-in, which lets data scientists discover new patterns and insights in healthcare data.
- Data protection—HyperStore provides data durability of 99.999999999999% (14 nines), by distributing data using replication or erasure coding. The number of replicas and erasure code schemes can be customized to meet the SLA.


